Enhancing AWS Security and Compliance with AWS CloudTrail
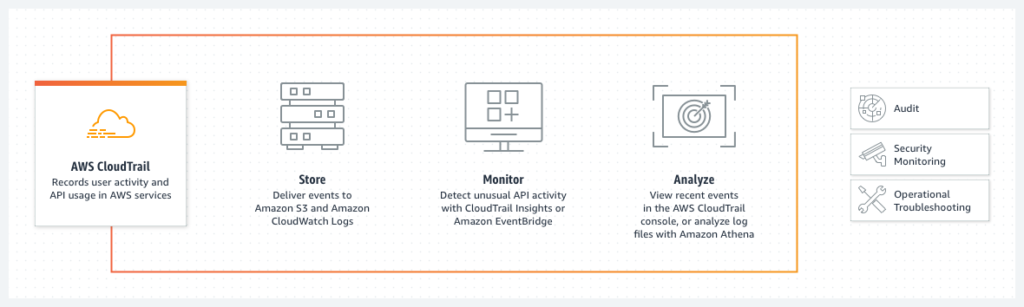
AWS CloudTrail is a powerful service that allows you to log, monitor, and analyze events and activities in your AWS account. With CloudTrail, you can track changes to your resources, monitor API calls, and detect security threats in real-time. In this blog, we will explore the features and benefits of AWS CloudTrail, and how it can help you improve the security and compliance of your AWS environment.
AWS CloudTrail is a service that provides a complete record of all events and activities in your AWS account. This includes API calls made by users, AWS services, and external applications. CloudTrail logs events to an Amazon S3 bucket, where you can analyze and review them using AWS tools such as Amazon Athena, Amazon QuickSight, and AWS Glue.
CloudTrail provides several benefits for AWS users:
1. Compliance: With CloudTrail, you can meet compliance requirements for audit and security monitoring. CloudTrail logs help you demonstrate compliance with regulatory standards such as PCI DSS, HIPAA, and SOC 2.
2. Security: CloudTrail logs can be used to detect and investigate security threats, such as unauthorized access, privilege escalation, and data breaches. CloudTrail logs also enable you to implement security best practices, such as identifying and removing unused IAM users and roles.
3. Troubleshooting: CloudTrail logs provide a complete record of changes to your AWS environment, which can help you troubleshoot issues and identify the root cause of problems.
4. Governance: CloudTrail logs can be used to enforce governance policies, such as ensuring that all resources are tagged correctly, and that changes are approved by the appropriate stakeholders.
How AWS CloudTrail Works
CloudTrail works by logging API calls made in your AWS account. This includes calls made by AWS Management Console, AWS SDKs, command line tools, and other AWS services. CloudTrail logs contain information about the identity of the caller, the time of the call, the source IP address, the request parameters, and the response elements.
CloudTrail logs are stored in an S3 bucket, where you can configure them to be encrypted and archived to Amazon Glacier for long-term storage. You can also configure CloudTrail to send logs to CloudWatch Logs, where you can monitor them in real-time and set up alarms based on specific events or patterns.
CloudTrail logs can be analyzed using AWS tools such as Amazon Athena, which allows you to query and analyze your log data using SQL, and AWS Glue, which allows you to transform and enrich your log data. You can also use third-party tools such as Splunk or ELK to analyze CloudTrail logs.
Best Practices for AWS CloudTrail:
1. Enable CloudTrail for all AWS accounts and regions: This ensures that you have a complete record of all events and activities in your AWS environment.
2. Encrypt your CloudTrail logs: Encrypting your logs ensures that they are secure and cannot be accessed by unauthorized users.
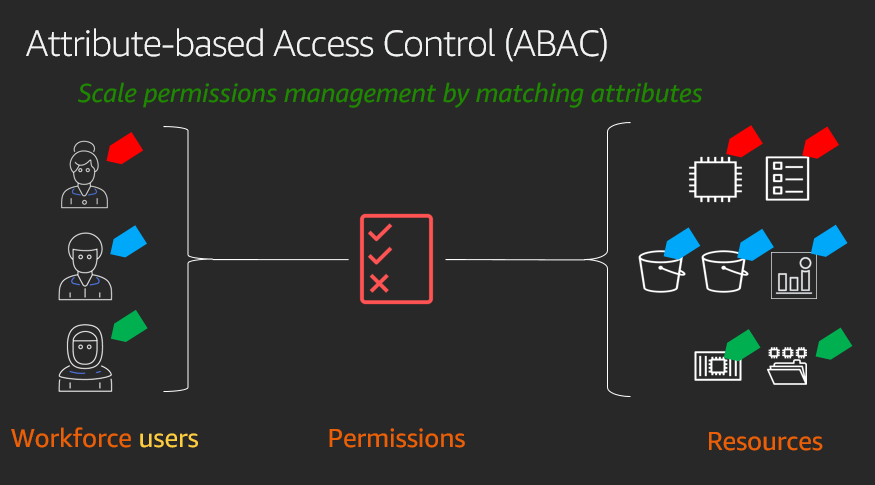
3. Use IAM roles to grant access to CloudTrail logs: IAM roles allow you to grant access to specific users or groups, and provide fine-grained control over who can access your logs.
4. Monitor your CloudTrail logs: Use CloudWatch Logs to monitor your logs in real-time and set up alarms based on specific events or patterns.
5. Archive your CloudTrail logs: Archive your logs to Amazon Glacier for long-term storage and compliance purposes.